How to Use a ClickOnce Signing Certificate in Visual Studio
87% of IT leaders interviewed by Zendesk have cybersecurity and data privacy at the top of their 2024 strategy. Explore how a ClickOnce signing certificate can elevate the security of your Visual Studio apps and reach the highest levels of customers’ trust
By the end of 2023, 61% of SecDevOps professionals interviewed by Cycode indicated the application attack surface grew to such an extent that it became unmanageable. That number was even higher for Chief Information Security Officers (CISOs) — 78%!
Do you develop your organization’s software applications using Visual Studio? If so, a ClickOnce certificate can help developers like you start 2024 on a different note and:
- Reduce the risk of malware infections and supply chain attacks for your customers, and
- Build digital trust and prove to customers that your apps are authentic and can be trusted.
This type of digital certificate, issued by a trusted certificate authority (CA), is based on asymmetric encryption (i.e., public key cryptography). Signing your applications with this technology enables you to assert your digital identity and protect your apps from malicious alterations.
Want to know more about it? In this first article of a three-part series, we’ll answer several critical questions concerning ClickOnce certificates:
- How a ClickOnce signing certificate works,
- What it does,
- Where to get it,
- How can you use it, and
- Why should you use it in Visual Studio?
How to Use a ClickOnce Code Signing Certificate
Want to add your digital signature to your application or code that was built in Visual Studio? Then you’ll have to sign the folllowing:
- Application manifest,
- Deployment manifest,
- Application files, and
- Bootstrapper files (i.e., setup.exe).
One option is to sign your application using a self-signed certificate. (NOTE: This should only ever be used for testing, never for production.) Another is to sign it using a publicly trusted code signing certificate. Doing this ensures that your certificate is valid for both testing and distribution.
There are various ways to sign your ClickOnce manifests using a code signing certificate. One of them is through the Visual Studio Publish Wizard.
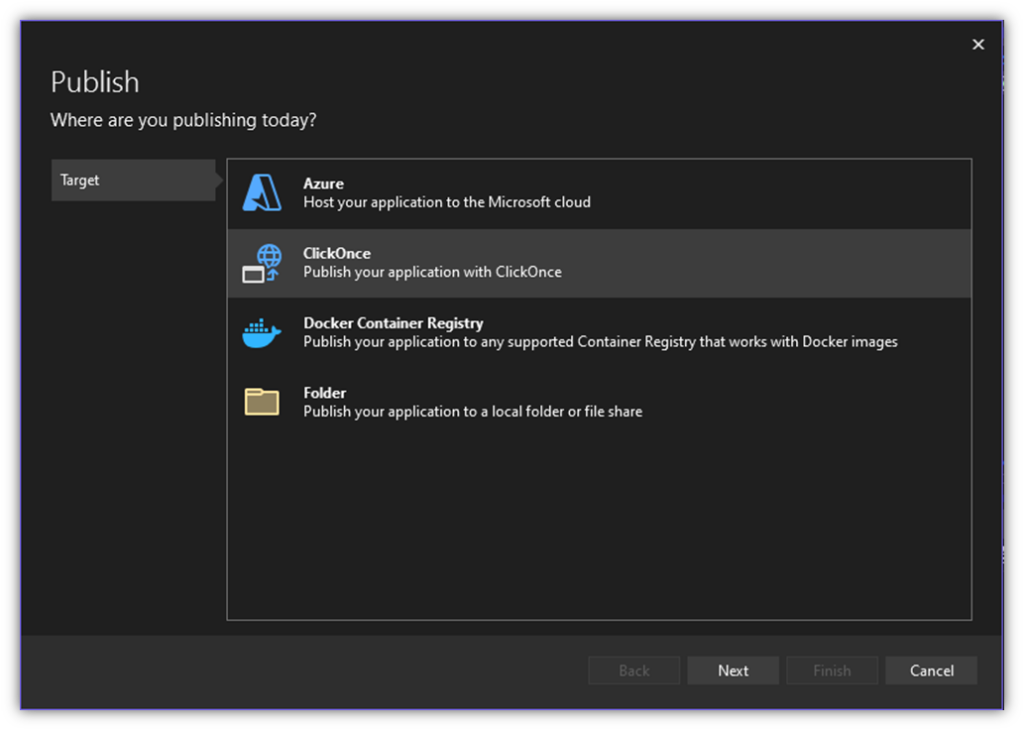
Once your application is ready, insert your secure hardware token in your device and, in Visual Studio click Publish to create your ClickOnce Publish Profile (in case you don’t have one already):
- Select ClickOnce as a target (or specific target) and hit Next.
- Go through the options to set your publication preferences, installation location, and settings until you reach the Sign Manifests section.
Here is where you can make the magic happen and finally get your manifests signed:
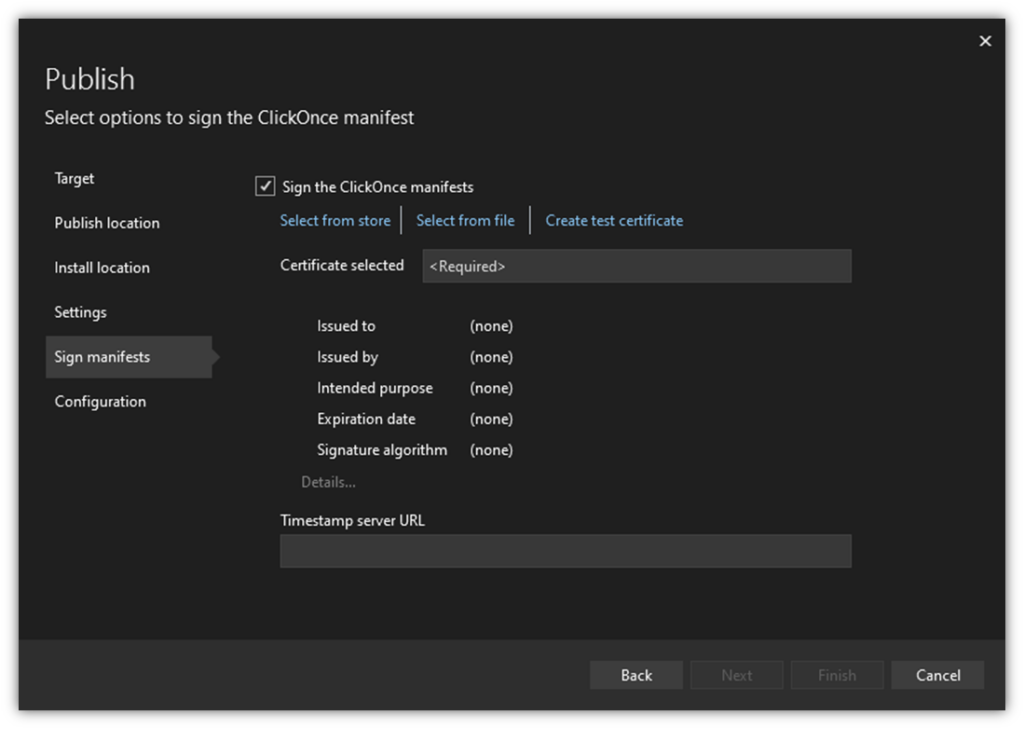
- Check the Sign the ClickOnce manifests option.
- Choose your signing certificate by clicking on “Select from store.”
- Add your certificate authority’s timestamp URL (this is optional, but strongly recommended as specified in our Pro Tip).
Pro Tip: A timestamp allows your digital signature to be trusted long after the ClickOnce certificate has expired. Thanks to this small (and free) operation, even if your certificate is expired, the operating system (OS) will still trust it and guarantee a seamless installation.
That’s it. Now, all you have left to do is to specify your project configuration and click Finish. This will close the window and a new summary page will appear. To initiate the publication of your project and get the other application’s files signed, click on the Publish button.
Is Visual Studio Having Issues Finding Your ClickOnce Certificate?
When you clicked on “Select from store,” did you get an error message stating that no certificates meet the application criteria? This is because Visual Studio currently supports only Rivest Shamir Adleman (RSA) certificates. This means that if you have the newer and more secure Elliptic curve cryptography (ECC) certificate, Visual Studio will have issues recognizing it.
The solution? You’ll need to reissue the certificate with an RSA key instead of an ECC key.
The process for reissuance will differ depending on which CA issued your certificate. Your CA or authorized certificate dealer can help you through the process. For those of you using DigiCert code signing certificates, you can follow our guide on how to set up your code signing certificate hardware token to reinitialize your secure hardware token. This will process will:
- Delete your existing ECC certificate, and
- Allow you to generate a new certificate using RSA. (Just be sure to select an RSA key size of 3072 bits. )
Now, back to the steps for ClickOnce signing…
Manually Sign Your Application Files and Executable
Did the ClickOnce wizard only sign the manifests and leave the other application files (e.g., .exe and .dll files) unsigned? No problem! You can still sign them manually, one by one. You can manually add your digital signature to each single file using PowerShell and Microsoft SignTool. (Click on these links to read more.)
So, now that you have an overview of how you can use a ClickOnce certificate, let’s find out:
- What it is,
- What its purpose is, and
- Where you can you get one.
What Is a ClickOnce Signing Certificate?
A ClickOnce certificate (i.e., a code signing certificate or Authenticode certificate) is a small file containing the digital identity information of an entity. There are two types of ClickOnce code signing certificates that you can use:
- A self-signed ClickOnce certificate. This is digital certificate that you generate yourself in Visual Studio. This certificate can be used for testing but won’t be recognized as being trusted outside your device or local network and will likely display errors when a user tries to run software signed by it.
- A publicly trusted ClickOnce code signing certificate. This type of certificate is issued by a publicly trusted certificate authority (CA) after a stringent validation process has vetted your digital identity. Once applied to an app, it uses public key cryptographic functions to:
- Authenticate the author (i.e., prove that they’re the legitimate creator), and
- Confirm that the software is safe and hasn’t been infected with malware.
Because you’ve signed the app using a publicly trusted code signing certificate, it’ll be trusted by users who download your app on the internet. This is because their systems will be able to verify through the certificate’s chain of trust that the certificate was issued to you, and that a trusted third party verified you.
Does a ClickOnce Signing Certificate Differ from Other Signing Certificates?
Not really. At a base level, they help secure the same things. People often call it a ClickOnce signing certificate because that’s what they’re using it for, but these certificates also can be used to sign many other things relating to software, including:
- Executables
- Apps
- Drivers
- Scripts
- Manifest files
Code signing certificates, including ClickOnce signing certificates, come in standard and extended validation (EV) options. While standard certificates enable you to display verified identity information in warning screens, EV certificates are automatically trusted and eliminate these warning messages.
How Do You Get a ClickOnce Code Signing Certificate?
Do you want to add a layer of security and protect the integrity of the software app you’re developing in Visual Studio, all in one go? Sign it using a publicly trusted ClickOnce code signing certificate. You can purchase one from a publicly trusted certificate authority (CA) or an authorized reseller.
Save Up to 27% on an Extended Validation Code Signing Certificate
Bolster trust in your brand and meet the Windows Hardware Developer Center requirement of having an EV code signing certificate. Certificates start at $250.00/year with a 3-year purchase.
Do you already have one? Excellent. Verify that your private key is stored on secure hardware (e.g., a USB token or a hardware security module). This has been required since June 2023, when the latest CA/B Forum’s new security code signing baseline requirements rolled out.
4 Jolly Good Reasons Why You Need a ClickOnce Signing Certificate
In a world where ransomware gangs are interviewed by mainstream journalists, winning (and keeping) customers’ trust as a legitimate software developer or publisher can be really challenging.
Code signing certificates may not be the cybercriminals’ kryptonite however, they’re one of the best weapons you could add to your cybersecurity arsenal as a software dev or publisher. Why? Because signing your Visual Studio-created applications with a ClickOnce certificate doesn’t only authenticate your software and provide tamper-proof protection. It also enables you to do the following:
1. Create a Verifiable Chain of Trust
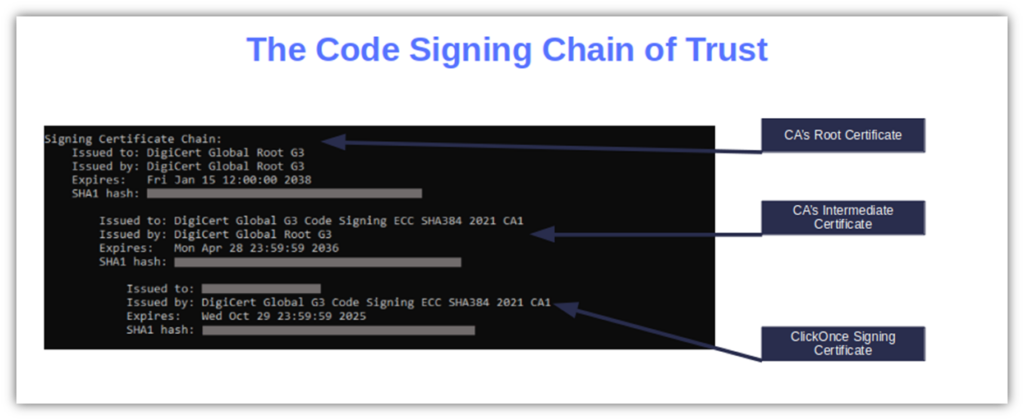
Trusted code signing certificates are a bit like a family tree. A signing certificate (called a leaf certificate) can be traced back to the original signing authority (i.e., the root CA). How? through the CA’s intermediate certificate (i.e., the link between the CA’s root certificate and your certificate).
If any part of this chain of trust is compromised, it breaks the trust chain and the user is alerted.
Did you sign your app with a self-signed code signing certificate? Bad idea. As the certificate has been generated by you, there is no chain of trust. OK, we know you’re a good developer and that your apps are malware-free (right?). But how can you prove it to your users when:
- You’re the one who has defined your own self-signed certificate policies.
- Operating systems and major web browsers like Google Chrome or Mozilla Firefox don’t recognize it as trustworthy?
The solution? Limit self-signed certificates to test environments and never use them for apps you’ll release to the public.
2. Guarantee Secure Software Distribution
Using a ClickOnce signing certificate offers assurance that your software distribution chain is secure and malware-free. (No one’s tampered with it since you signed it because the signature’s hash value would otherwise be altered.) In addition, you’ll be able to distribute your applications through Microsoft’s official channels, such as Microsoft Store.
Do you want to offer a completely automated installation of your application that doesn’t require user interaction? Use your ClickOnce certificate to include your signed applications to the list of trusted publishers. Boom. It’s done.
3. Reduce or Outright Eliminate Pesky Warning Messages
Ever seen messages like “Unknown publisher,” “Windows requires a digitally signed driver,” No signed device drivers were found,” and “Do you want to allow this app to make changes to your device?” These are just a few alerts besetting Windows users who try to install unsigned software.
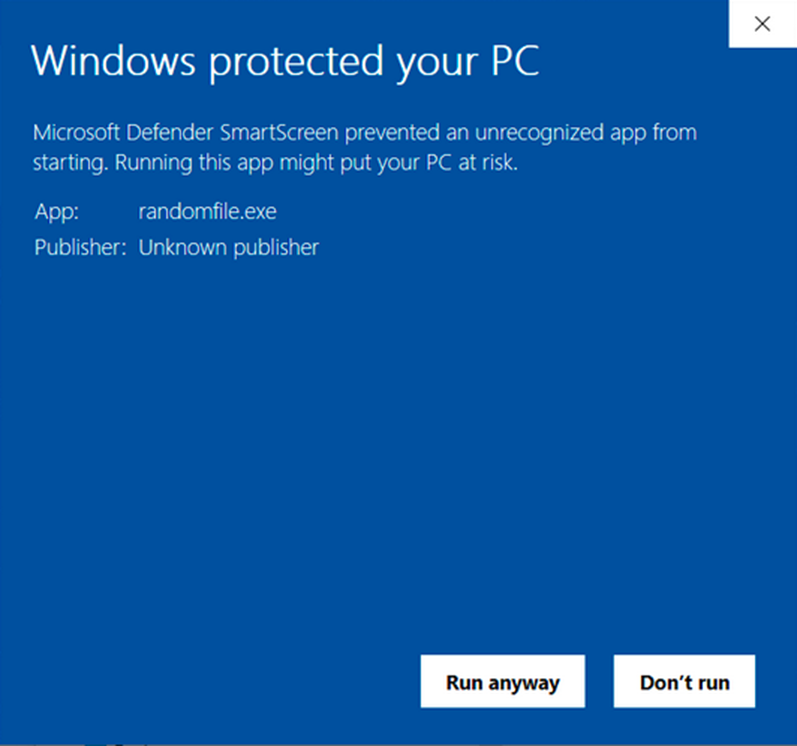
The cheapest standard code signing certificate (also known as an organization validation [OV] certificate) will reduce the notifications to the minimum. Signing your software using an extended validation certificate (EV) instead will completely eliminate these Microsoft Defender SmartScreen warnings because the software will be trusted automatically.
Make your choice wisely, and guarantee your users a smoother installation experience.
4. Beef Up Brand Reputation and Bolster Downloads and Revenue
A 2023 report from ThreatX shows that 60% of consumers in the U.S. are reluctant to do business with a brand that’s had a security issue. The same percentage would happily pay premium dollars to buy from an organization that shows it’s invested in data privacy and security.
A ClickOnce certificate is your best bet to enhance customers’ confidence in your products. It’ll put the spotlight on the security and integrity of your software, thereby amplifying your potential download rates. And who wouldn’t like to start a new year in a higher gear and supersize profits?
So, how can you infuse the power of a ClickOnce signing certificate into your Visual Studio application development process? Let’s uncover the arcane.
How ClickOnce Signing Certificates & Visual Studio Ensure App Integrity & Authenticity
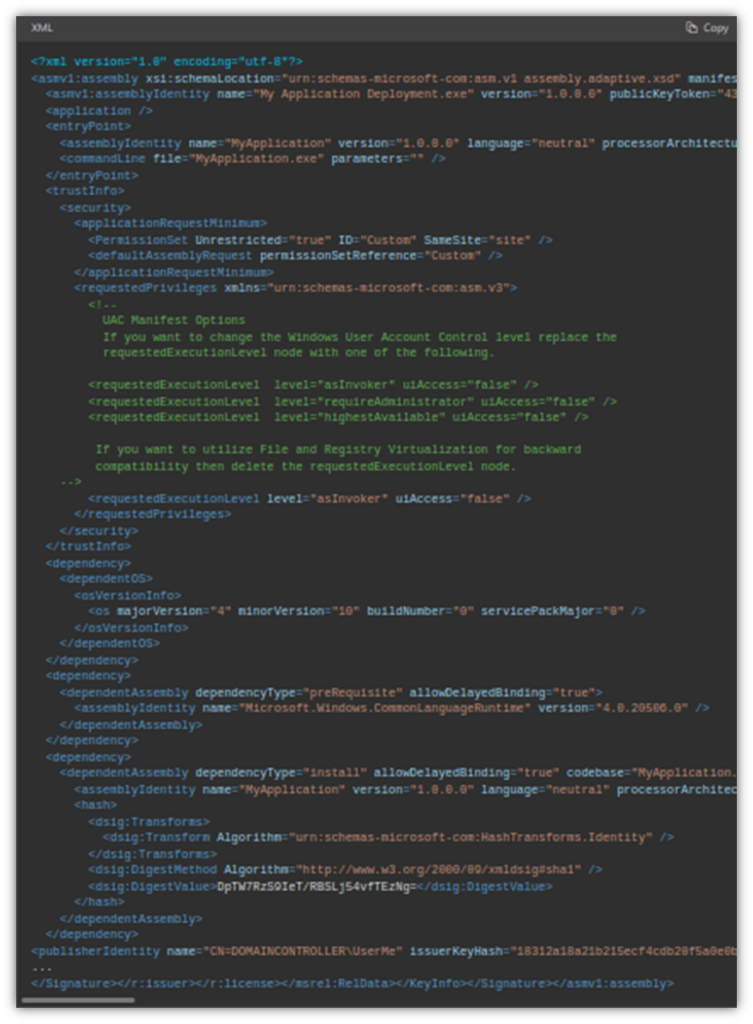
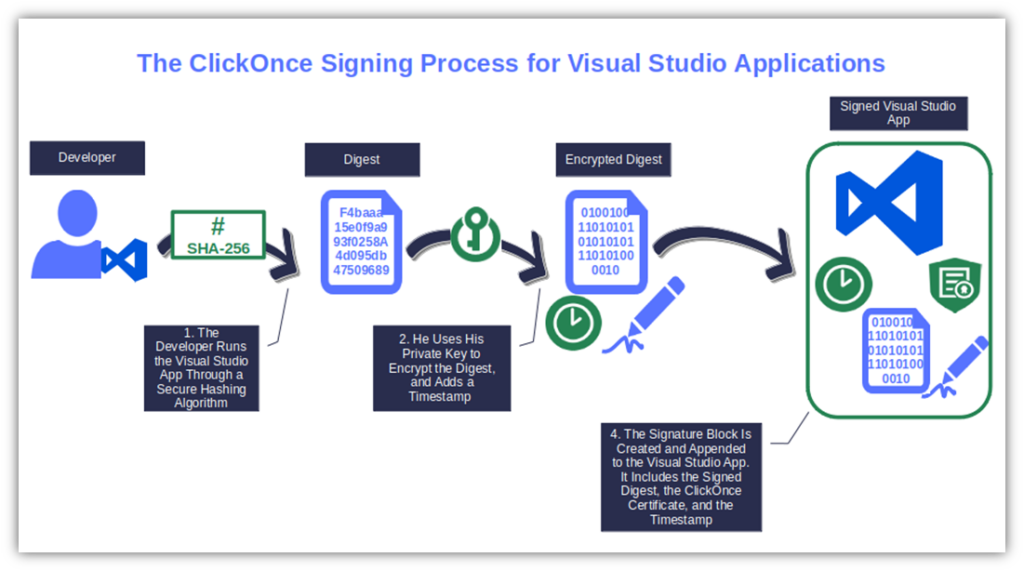
To put it briefly, when you sign your ClickOnce manifest with a code signing certificate, the software is hashed using a strong hashing algorithm. Next, the hashed value (i.e., a unique fixed-length string also called digest) is encrypted with the private key that’s stored onto your secure hardware token.
Finally, the signature bundle is created including:
- The hash function,
- The encrypted digest,
- The timestamp (optional but recommended), and
- The ClickOnce signing certificate (i.e., code signing certificate).
From now on, every time a user will attempt to install the published app, their client will:
- Use the public key to decrypt the signature (authenticity and identity verification),
- Generate a new digest based on the downloaded application, and
- Compare the original digest with the newly created one (software integrity).
Hocus pocus! The installation will continue only if the two digests match.
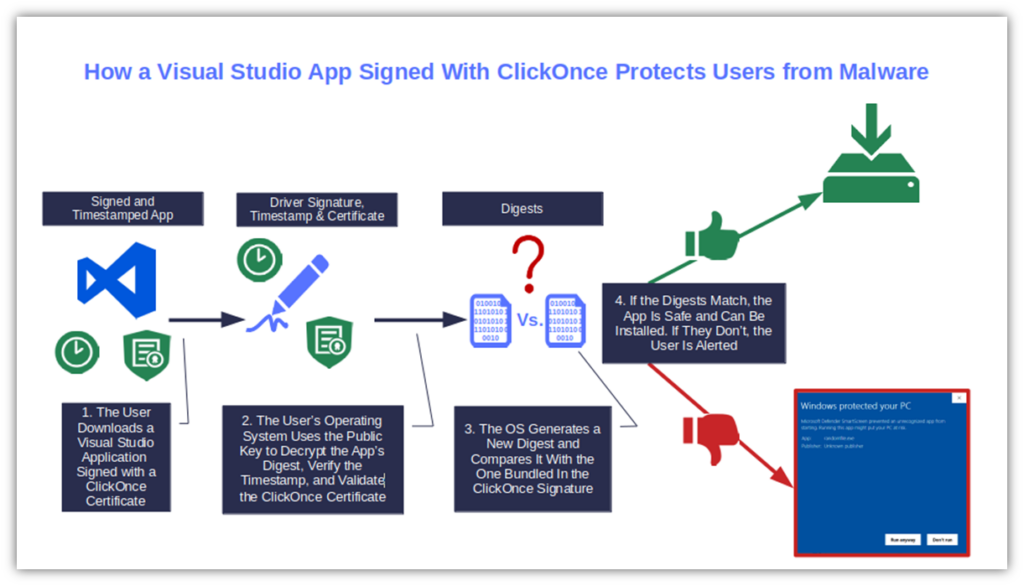
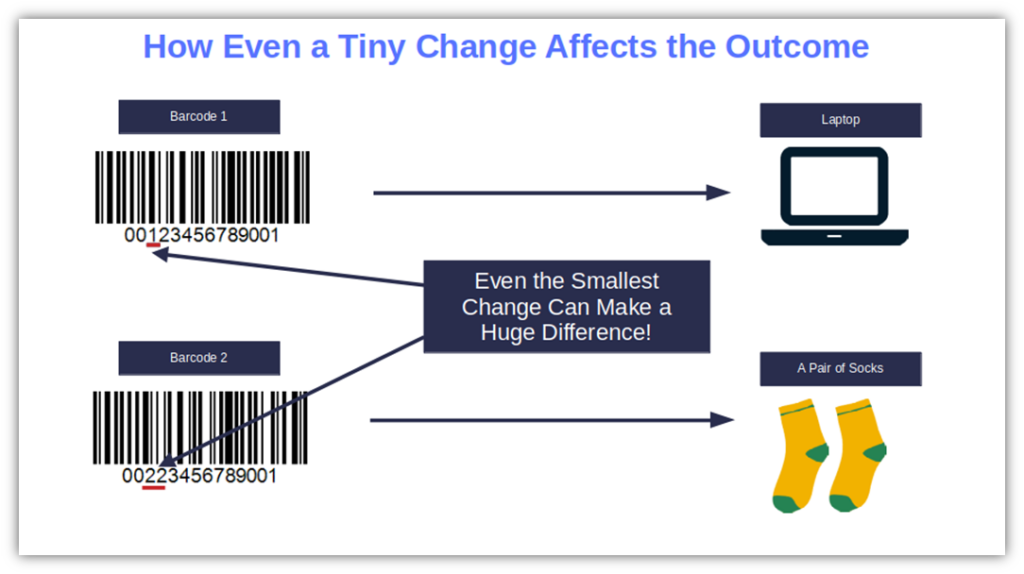
But what if you digitally sign your application but then an attacker manages to compromise your application? After all, using a code signing certificate doesn’t prevent anyone from changing your code. However, it does provide a checksum that systems can use to verify whether the code is authentic and unchanged, and if someone has modified the code since it was signed.
When you hash your file as part of the digital signing process, even a small change made to the original code will generate a totally different digest, meaning that the original file and modified file’s hashes won’t match. Thus, the user will be alerted, and the installation will be stopped. This is why code signing can help save your software users from malware infections.
One of the features that makes code signing and timestamping even more attractive is Visual Studio’s integration of it in the development process that we mentioned at the beginning of this article.
Yes, sometimes, Visual Studio integrated developed environment (IDE) can get tricky, and it isn’t always bug-free (then again, what software is?). Nevertheless, in 2023, it was still the second favorite IDE by developers surveyed by Stack Overflow, just after Visual Studio Code.
Thanks to code signing and the ClickOnce manifest signature, software developers and publishers can boost the security of the app they’ve just created and certify its integrity and authenticity.
So, what do you think? Did this “sneak peek” into ClickOnce signing tantalize your curiosity? Want to learn more about it? Bear with us. In our next article, we’ll put together an in-depth guide on how to sign ClickOnce manifests.
Save Up to 27% on a Standard Code Signing Certificate
Assert your organization’s verified digital identity to increase trust in your software and updates. Boost your sales and download rates for as little as $195.00/year (with a 3-year certificate).
Final Thoughts on How to Use a ClickOnce Signing Certificate in Visual Studio
Using ClickOnce signing certificates in Visual Studio will attach your verified digital identity to your newly developed software applications. It’ll ensure your code’s integrity, help provide a seamless user experience, and boost your brand reputation by eliminating scary warning messages and unsigned software-related errors.
To get the best from it, don’t forget to:
- Timestamp code when signing, and
- Securely store your token when it’s not in use.
Now that we’ve taken you through the theory and revealed the magic behind ClickOnce certificates, it’s time to jump to the next level. Don’t miss our next article of the series, where we’ll teach you how to sign a deployment manifest with a ClickOnce certificate.


