Windows Has Blocked This Software Because It Can’t Verify the Publisher
In 2022, Google Play and App Store hit the mark of 142 billion downloads. Have you just downloaded software and Windows blocked it because the publisher could not be verified? Are your customers complaining about the same security warning when trying to install your new app? Discover what lies behind this error and how its tie to malware and digital trust could impact users and organizations alike
From September to the end of November 2022, Blackberry reports it stopped 1,757,248 malware-based attacks in just 90 days. The research also shows that cybercriminals were creating, on average, a new piece of malware every minute that can be used to attack businesses and other organizations globally. Another report from DigiCert, a publicly trusted certificate authority, says that 84% of the customers they interviewed would consider changing vendors if they lost trust in a company and its ability to protect their sensitive data.
But what do these two very different elements, malware and trust, have to do with the error message “Windows has blocked this software because it can’t verify the publisher”? And what does this warning mean?
If you’re intrigued, then stay tuned. In this article, you’ll find the answers to these two questions. Spend a few minutes of your time learning:
- What the error message means and why it’s directly linked to malware and customer trust.
- The consequences for your organization and you as a user if you’d decided to ignore it.
- How to deal with this warning (and others like it).
Because as Benjamin Franklin said, “An investment in knowledge always pays the best interest.”
What Does the Message “Windows Has Blocked This Software Because It Can’t Verify the Publisher” Mean?
Eureka! You’ve finally found the software you need that’ll enable you to save time and be more efficient in your tasks. But when you try to install it, a pop-up appears in your Internet Explorer browser: “Windows has blocked this software because it can’t verify the publisher.”
But wait, Internet Explorer no longer exists! That’s true, but you’ll also come across similar warning messages in other browsers and Windows operating systems as well. For example, we’ve written about the unknown publisher warnings that appear when you try to install software from creators whose identities your device’s OS or browser can’t identify.
Bummer! You really thought you finally found the solution to your problems, and now this rotten machine won’t let you install it. Why? Every time you try to install a new application, Windows validates its authenticity to protect your device from malicious software. How? By checking:
- The code’s digital signature. This is a digital stamp that uses cryptography to bind the publisher’s organization to the code.
- The digital certificate. Also called a code signing certificate, it’s a small file asserting the identity of the publisher and the integrity of the file.
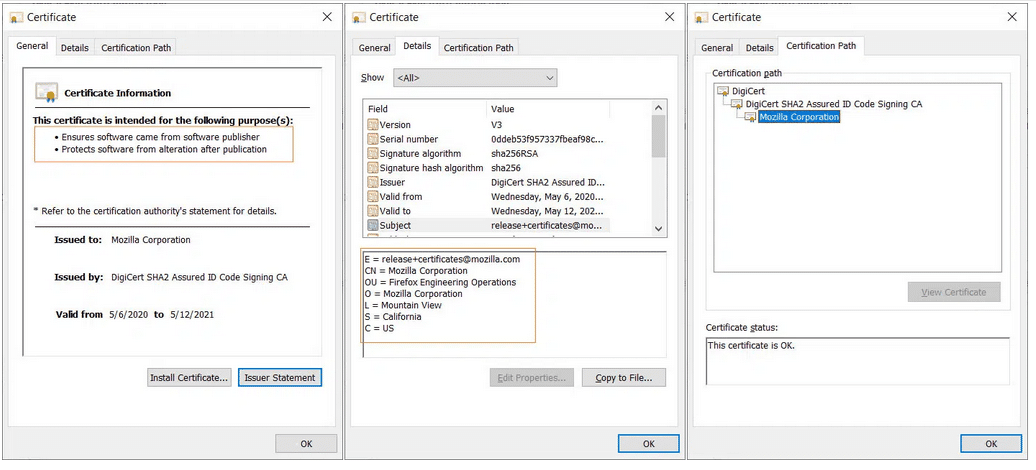
There are a couple of reasons why the validation can fail. For example, the digital signature and the code signing certificate are missing (i.e., the code is unsigned), or the certificate is invalid (e.g., it expired or it has been tampered with). Regardless of the reason, your Windows device will show you that very security warning, informing you that the publisher could not be verified.
From this perspective your Windows device doesn’t look so rotten anymore, right? After all, it’s trying to protect you from an unknown enemy. Hold on, does it mean you couldn’t install that software for one or both of the following reasons?
- The publisher wasn’t as trustworthy as you thought, or
- The code was modified by a cybercriminal?
Yup! That’s correct. The error messages “Windows has blocked this software because it can’t verify the publisher” and “the publisher cannot be verified” are both “computer-speak” for a device or browser recognizing that there’s something wrong with the software you downloaded and tried to install. Therefore, no matter how you put it, it’s now clear that every time you see it, the last thing you should do is ignore it. Even if you’re 100% positive that the code you’re trying to install is safe. Why? This is what we’re going to explore next.
Before we do, though, let’s point out just one more thing. What if you’re like me and you’re using a Linux-based device or a Mac? Or, what if you simply used a different browser (e.g., Firefox, Chrome, or Brave)? Would you also get a warning message?
The answer is yes, you would. The text would be slightly different. For example:
- Firefox has prevented this site from installing an unverified add-on.
- You are attempting to install an add-on from xyz.com. Make sure you trust this site before continuing (Firefox).
The screenshot we captured that shows one of the security warning examples from Firefox.
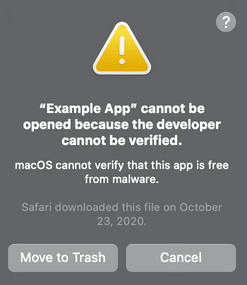
Even if the phrasing of each message differs from one to the next, the basic meaning behind all of them wouldn’t change.
Why Ignoring Windows Warnings That a Publisher Can’t Be Verified Is Never a Good Idea
A few months ago, one of my neighbors asked me if I could help him to reinstall his laptop’s operating system. He told me his device had been infected with a nasty virus. To get rid of it, he had to completely wipe the hard drive.
This surprised me. Even though the guy wasn’t a tech guru, he was no stranger to technology, and he surely knew how to avoid malware infection. Being nosy, I asked him what had happened.
He said he downloaded software from a known website and that the installation was blocked by the “usual and annoying” (so he said) Windows browser warning, stating the publisher could not be verified. At that point, he did what he always did: he used a workaround he found on the internet and installed it anyway. The only difference is that this time, the software he downloaded came with the infamous LockBit ransomware, locking all his files and rendering the machine completely unusable.
To keep the story short, it took us the whole afternoon to get the laptop up and running again. Luckily enough, my friend had backed up his files before installing the code, so he basically recovered virtually everything.
He learned the hard way that downplaying Windows alerts can spell disaster. Since that incident, he now never disregards Windows security warnings.
OK, maybe it won’t happen to you however, there are more reasons why you, as a user or as a developer/vendor shouldn’t ignore the publisher could not be verified error. For those in a hurry, we’ve summarized a few hints in the table below. Keep on reading through if you can! We still have much more to say on this topic.
| What the “Windows Has Blocked This Software Because It Can’t Verify the Publisher” Warning Means to You | |
|---|---|
| User | Developer/Vendor |
| Protects you against downloading malware-infected software. | Protects you and your organization from downloading and/or spreading malware. |
| Minimizes the risks of data breaches. | Reduces the risks of data breaches. |
| Makes it more difficult for attackers to steal your credentials.. | If it comes up when your customers are trying to install your codes, it may reduce their trust in your brand, and it’ll harm your reputation. |
| If the customers are unable to install your add-ons because of the security warning, you’ll end up with fewer downloads and lower sales. | |
Users: Why Should I Care About the Warning “Windows Has Blocked This Software Because It Can’t Verify the Publisher”?
If you’re still unconcerned, let me give you a few other good reasons why you should be careful.
Malware Infections
OK, we’ve just talked about it however, there’s more. Did you know that between January and the first week of February 2023, AVTest identified a stunning 9,015,823 new pieces of malware?
This makes it an average of 231,175 new malware a day. Do you still think that the chances of your device getting infected are so meager? Maybe. But if it gets infected, it’ll take a while to clean up the mess.
Data Breaches
The Identity Theft Resource Center’s (ITRC) 2022 data breach report shows that in the U.S. alone, data breaches have affected at least 422 million people. Surprise, surprise, malware infection was one of the most common attack vectors, impacting 4.3 million victims. How did cybercriminals manage to harvest data from so many people?
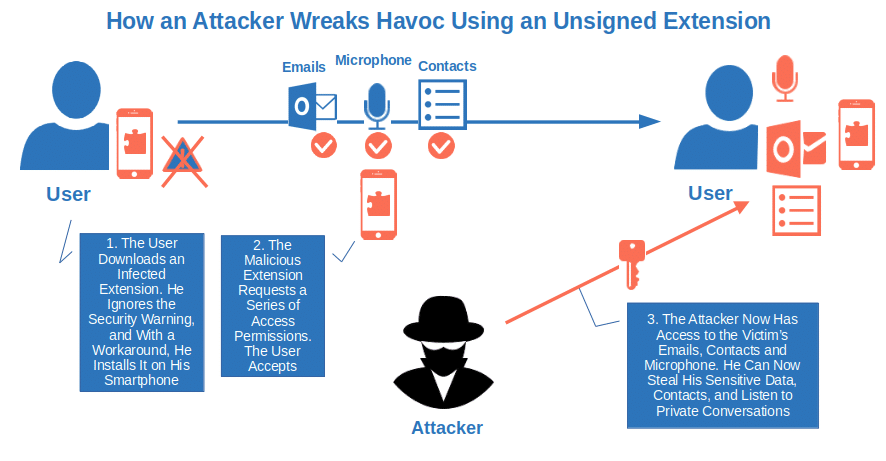
Let’s say you did like my neighbor, and you downloaded a new browser extension from an unverified publisher. During the installation, the extension asks you for access permissions to stuff on your device (e.g., to use your microphone or access your contacts, send messages — you name it). Without thinking twice, you accept.
Congratulations! You’ve just given access to all that to an attacker. He can now easily steal your sensitive data and your friend’s email addresses. And, why not? It can even listen to your private conversations.
Stolen Credentials
Did you know that in 2021, the Photon Research Team at the tech startup Digital Shadows, counted more than 24 billion usernames and passwords up for sale in the dark web (i.e., the “dark side” of the internet where cybercriminals engage in their illicit activities)? That’s a 20% increase compared to 2020.
And guess what? The same whitepaper confirms that info-stealer malware (i.e., malware that once installed on your device sends data, credentials and cookies to the attacker) can be found for sale at as little as $50. That’s right! You don’t have to be rich (as Prince said in his song “Kiss”) to steal credentials.
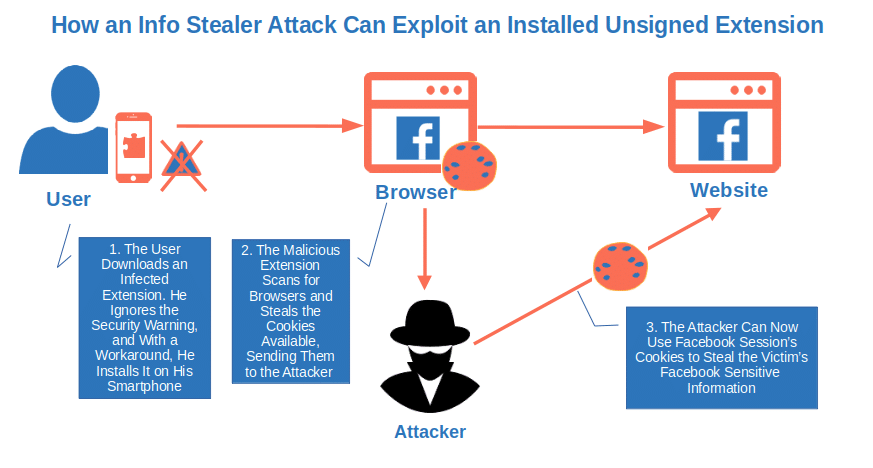
How big is the risk for your device if you’d ignore the “Windows has blocked this software because it can’t verify the publisher” warning message? Pretty high. In fact, Accenture’s Cyber Threat Intelligence team (ACTI) found that the information stealer malware has become a hot topic since 2022 while new versions of the malware are being discovered by the day (e.g., Vidar, Graphiron, and Titan).
I guess this is enough to convince even the more skeptical individual that disregarding a security warning informing you that the publisher could not be verified isn’t a wise thing to do. And if you’re an organization or an independent developer, the consequences could be even worse. Want a few examples? Read on.
Developers/Vendors: Why I Shouldn’t Overlook the Warning “Windows Has Blocked This Software Because It Can’t Verify the Publisher”
Now, let’s see this issue from a developer/organization perspective and understand what’s at stake here.
Increases the Risk of Malware Infections
Yup! Here we go again. If you think that one infected machine was bad enough, you haven’t seen anything yet. Let’s go back to my neighbor’s ransomware infection. Yes, it took him a whole afternoon to reinstall his system, but once done, he was up and running again. But let’s scale things up a bit…
Imagine what would have happened if the infected device was part of a network of computers used in an organization. Within minutes, the malware would have spread to other devices on the same network, causing real havoc. And that’s not all…
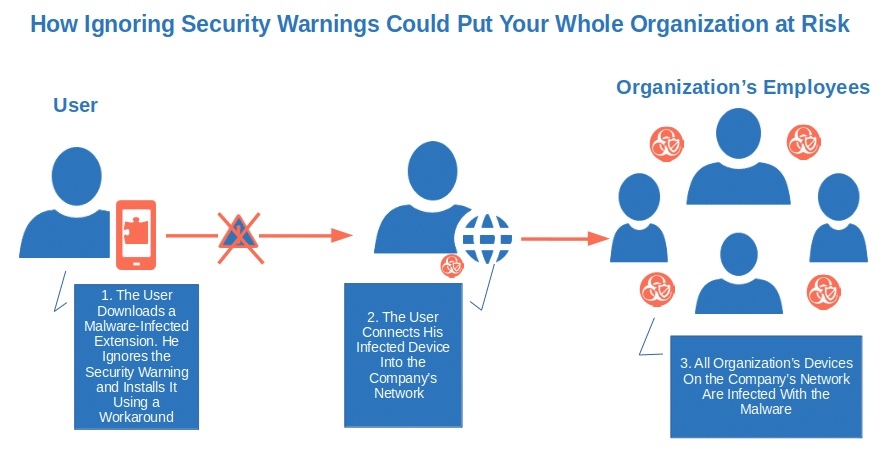
According to the latest data from IBM, an organization would have had to fork out an average of $4.54 million to recover from a ransomware attack. A destructive attack would be even worse. All organization’s systems would become totally inoperable and nearly impossible to recover. That’s why IBM’s data shows such malware infection could cost businesses even more ($5.12 million).
Data Breaches
The same IBM report also shows that in 2022, organizations victims of a data breach took an average of 277 days (i.e., nine months) to spot and contain a breach. Translated into financial terms, it represents a global average cost of $4.35 million and $9.44 million for a U.S.-based organization. That’s a lot of money.
But containing a breach isn’t the only cost that a business will have to face. Have you ever heard of the European Union’s General Data Protection Regulation (GDPR)? If your organization is the target of a successful data breach, you may have to pay a hefty fine. You aren’t affected by this regulation? Don’t celebrate yet. There are other regional or industry-based regulations that might impact you.
And, if cybercriminals managed to get hold of your customers’ sensitive information during an attack, you may also have to bear the costs of legal action against your organization. And this takes us to the next point.
Lower Customer Trust and Poor Reputation
A 19th-century English proverb says, “Give a dog a bad name and hang him.” In other words, if a person’s reputation (or, in our case, an organization’s reputation) has been stained, they’ll have a hell of a hard time cleaning it up.
How would you think a customer would react if, when trying to install your add-on, they saw a security warning stating that “Windows has blocked this software because it can’t verify the publisher” (or something equally scary)? I tell you what I would do in their shoes:
- I’d lose trust in the developer or publisher.
- I’d spread the word by adding negative feedback online and warning my friends and colleagues about it.
Do you think your customers won’t do the same? Think again. A report by the Institute of Customer Service shows that your expectations and customers’ responses may not align:
- 67% of clients who don’t trust a business would switch to a competitor and discourage their peers from using that company.
- 78% would actively look for a different company to work with.
- 55% would leave a negative online review for the company.
What are the natural consequences of lower customer trust and a poor reputation? Check out the next point to find it out.
Fewer Downloads and Sales
If you’re familiar with other Windows SmartScreen security warnings, like the “Unknown Publisher” warning, for example, you probably know that you can proceed with the installation anyway by clicking the button “Run Anyway.”
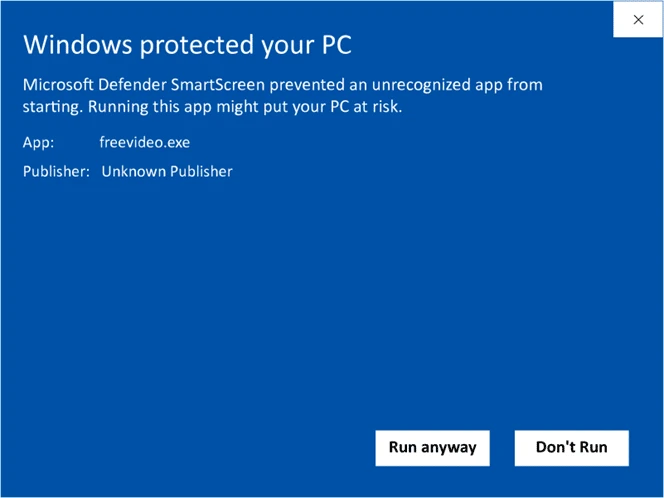
On the other hand, when you used to get the “Windows has blocked this software because it can’t verify the publisher” alert, things weren’t so easy, either. The pop-up didn’t offer you an alternative. Yes. there are workarounds available on the internet, however, they aren’t something your grandma or the average user would do easily.
To see it with my own eyes, I experimented. I sent four of my friends a link to an unsigned add-on for their Windows browser. I then invited them to install it. Bear in mind that they’re all average users utilizing their devices for emails, online shopping, banking, and a few other common tasks, but that’s about it. What do you think happened?
- Two gave up after their first attempt. When I asked them about the error message, they said they didn’t read it.
- One asked me if she was doing something wrong, but didn’t bother figuring out how to fix the error and gave up anyway.
- The fourth one told me that he didn’t install it because he never trusts software that gives him error messages during installation.
There you have it. No one installed it at the end (and rightly so). Three gave up even before trying to understand what was wrong with it. That’s great from a security perspective, but it’s bad news from a reputational one because people will be less likely to trust your products in the future.
Nowadays, people don’t have the time or patience to look for solutions. If the download doesn’t work, either they do without or look for an alternative that they can install without the hassle. When you break their trust, they simply go elsewhere. In fact, 55% of the respondents to Adobe’s 2022 trust report confirmed that they’d never spend a dollar doing business with a company that broke their trust. Can you see your sales and the number of downloads going down?
Last but not least, don’t forget that major software platforms don’t accept unsigned add-ons or codes, further restricting the size of your audience and potential customers.
Still unconvinced? Find out you could easily become the next hacker attack victim statistic when using or publishing unsigned code.
The solution to all this? It’s easier than you think.
How Can You Fix the Error Message “Windows Has Blocked This Software Because It Can’t Verify the Publisher”?
Every problem has a solution. You just have to find the right one. Let’s see what your options are in case your browser has blocked an installation because the publisher could not be verified.
Users: How Can I Solve the Error: “Windows Has Blocked This Software Because It Can’t Verify the Publisher”?
I just searched on Google for “How can I fix the error Windows has blocked this software because it can’t verify the publisher” and found about 749,000 results.
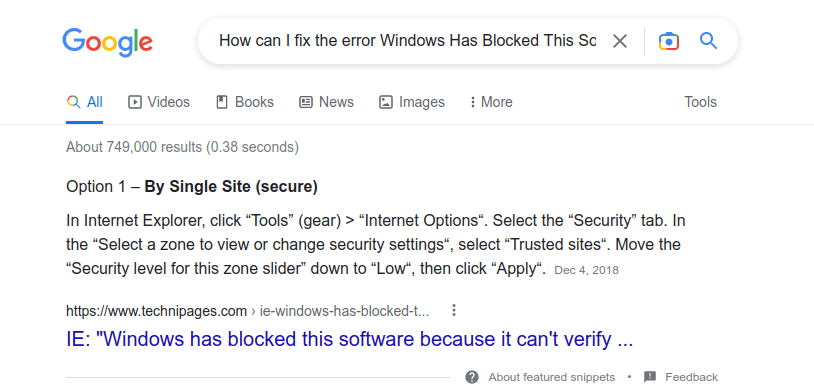
That’s many potential solutions to choose from. To ensure that you won’t experience any of the consequences we’ve just listed, the best solutions would be:
- Don’t install any software or code showing a security message. This is pretty straightforward. Avoid dodgy installation and you’ll be safe. There are so many software and add-ons available that you’ll surely find a replacement for that sketchy code. And now that you know the consequences you could face, do you still think that’s really worth the risk?
- Contact the vendor before installing it. Are you positive that the code you want to install is legitimate and malware-free? Before running into trouble, contact the vendor and warn him about the security message you’re getting. He may already have a solution or may be working on a fix.
Were you looking for a workaround that’d allow you to unblock the installation? Sorry, you won’t find it here. You’re free to look for it on the internet; however, you won’t get it from me. As a cybersecurity professional, I’d never recommend anyone to bypass a security warning. It would be like offering you a praline from a box full of chocolates knowing that among them there’s one filled with arsenic. No Russian roulette here!
Developers/Vendors: How I Can Avoid My Software Displaying the Error “Windows Has Blocked This Software Because It Can’t Verify the Publisher”
At the beginning of this article, we learned that this warning message — along with some of the other examples we talked about — is shown when there’s something wrong with the digital signature of the software. For example, if it’s been tampered with or the code simply isn’t verified/signed. What can you do then?
Sign your code, software or other executables with a code signing certificate issued by a trusted certificate authority (CA). It’s as simple as that. How?
- Pick a code signing certificate. You can choose between the organization validation (OV) or the extended validation (EV) code signing certificates.
- Get your organization validated by a trusted CA.
- Install the certificate on your Windows machine.
- Sign your codes.
There you have it! Now you can say goodbye not only to the detrimental security warning “Windows has blocked this software because it can’t verify the publisher” but also to the “Unknown Publisher” message.
And for those who really can’t stand Windows SmartScreen pop-ups, make sure you sign your codes with an EV code signing certificate. Your software will be immediately trusted by browsers and operating systems alike. Farewell, Windows SmartScreen! Your users won’t have to see that message ever again when installing your software.
Interested in learning more about code signing? The National Institute of Standards and Technology (NIST) published a detailed whitepaper: Security Considerations for Code Signing.
Lastly, here are a few pro tips:
- Add a time stamping to your signature. It’ll be considered valid even if the code signing certificate you used is expired. Want to know more? Check out our article about time stamping.
- Ensure you securely manage your code signing certificates and keys.
- Don’t use self-signed code signing certificates in production.
Final Thoughts on Windows Has Blocked This Software Because It Can’t Verify the Publisher
Nowadays, threats are lurking behind every corner, facilitated by the increasing availability of cybercrime-as-a-service offers on criminal marketplaces. With malware-as-a-service, for example, wannabe attackers can buy ready-to-use malware and/or malware deployment services — no hacker experience is necessary.
This is why you, as a user, can’t afford anymore to assume that the software you downloaded is safe or, even worse, bypass warnings like “windows has blocked this software because it can’t verify the publisher” and install it anyway. You may find yourself downloading the wrong application and wind up finding yourself up a certain creak without a paddle.
The same applies to software development organizations. Paying no attention to this security warning and continuing to publish unsigned codes isn’t a good idea. In the long run, your customers may consider your products insecure (even if they aren’t) and switch to the competition.
So, from now on, don’t ignore this error message. Maybe the code you’ve just downloaded is safe, but would you really bet the security of your device, sensitive data, or even your organization’s reputation on it?


