What Is a Software Testing Strategy and What Should It Cover?

Looking to strike the perfect balance between speed, quality, and costs like 40% of QA teams? Prepare your software for a successful launch by learning everything you need to know to create a rock-solid software testing strategy.
Is your software secure and trustworthy? According to CISCO, 94% of organizations confirmed that customers wouldn’t buy from them if their data wasn’t protected enough. This sentiment comes as no surprise when you consider how many data breaches make the headlines every week. Trust has become a big issue for customers in the last few years, and rightfully so.
A bad review regarding the security of one of your products, a glitch on your website, or — even worse — a data breach is enough to negatively impact your reputation and kill sales. How can companies mitigate these risks when a whopping 40% of software vulnerabilities are caught in production instead of being identified during testing?
A robust, well-built software testing strategy can help you cross T’s and dot I’s regarding your software’s security. It can help you ensure your product is secure and works as expected, even in the most unexpected scenarios. Let’s look under the hood at what a software testing strategy is, explore its potential, and the essentials it should cover to transform your testing procedures into winning actions.
What Is a Software Test Strategy?
The software test strategy is a document and approach to software testing. This resource includes a collection of guidelines explaining exactly how all organization’s applications and software tests must be designed and performed. In simple words, it provides a standardized approach to the whole software testing process.
So, is it just another document used by the quality assurance (QA) team to keep management happy? Not really. A software testing strategy is both the document and thought processes that’ll:
- Guide testers through the software testing process to achieve their goals most efficiently,
- Ensure that everyone involved in the organization’s projects is on the same page and part of the conversation,
- Answer stakeholders’ questions and set expectations for the team and project as a whole,
- Improve the quality of your code,
- Save time and money by helping you identify vulnerabilities and bugs earlier in the software development life cycle (SDLC),
- Accelerate the time-to-market of your software, and
- Increase collaboration among secdevops teams thanks to continuous feedback.
Created before the test plan, it’s a key part of the software testing life cycle (STLC), which is a crucial component of the SDLC.

With 84% of codebases containing at least one known open-source weakness, a software testing strategy will be your guiding light through the storm of vulnerabilities, malware, and bugs. It’ll ensure quality, efficiency, and reliability of tests by answering the following fundamental questions:
- What must be achieved? (This question should be answered both from an overarching perspective and also address specific goals and actions.)
- When must these items be achieved (i.e., this gives you a timeline so you can plan accordingly)?
- How will you achieve those goals (i.e., what’s the best approach)?
Hold on, isn’t the test plan answering these questions, too? Does it mean that testing plans and software testing strategies are the same thing? Not quite — let’s explore their key differences.
Software Test Strategy vs. Test Planning: An Overview of the Differences
The software test strategy and the test planning have the same final goal: to ensure the software works as planned. How they achieve it, though, is based on very different things. Which ones? Let’s explore the key ones listed in our table below:
| Software Test Strategy | Test Planning | |
| What Is It Based On? |
|
|
| What Kind of Document Is It? |
|
|
| Who Creates It? |
|
|
| What Does It Define? |
|
|
| When Is It Written? |
|
|
| Can It Be Updated? |
|
|

Got the differences? Now, let’s explore the most widespread types of software testing strategies available so that you can pick the right ones for your projects.
The 7 Most Common Types of Software Testing Strategies

Did you know that there are several types of software testing strategies? Each addresses slightly different needs, risk levels, and software development models (e.g., Agile, Waterfall). To help you choose the right one for your organization or product, we’ll look at the seven trendiest, one by one.
Would you rather skim the content of this section and quickly move on to discover the essentials that a best-of-breed strategy can’t do without? Then you should take advantage of our summary table below. But remember, as Andy Gilbert, the American baseball player and coach once said, “You can’t catch the big fish by skimming the surface.” This is why we have more in-depth information for our other readers. This next section will cover the seven software testing strategies outlined by LambdaTest.
| Software Testing Strategy | Testing Method Definition | Examples of Factors It Should Address | When It’s Mostly Used |
| 1. Methodical Software Testing Strategy |
|
|
|
| 2. Reactive Software Testing Strategy |
|
|
|
| 3. Analytical Software Testing Strategy |
|
|
|
| 4. Standards or Process Compliant Software Testing Strategy |
|
|
|
| 5. Model-Based Software Testing Strategy |
|
|
|
| 6. Regression-Averse (or Regression-Based) Software Testing Strategy |
|
|
|
| 7. Consultative Software Testing Strategy |
|
|
|
1. Methodical Software Testing Strategy
Are your tests going to be focused on the security of the application or on specific standards? If your answer to either is yes, then this is the testing strategy for you. A methodical software testing strategy is an approach that’s based on predefined test conditions and standards created by developers, quality standards, and checklists across multiple application versions. If specific needs aren’t met, then the testing will fail.
It’s often used for achieving compliance with the following:
- Privacy and security regulations. Such as the Payment Card Industry Data Security Standard (PCI DSS) the EU General Data Protection Regulation (GDPR), and the California Consumer Privacy Act (CCPA).
- Software quality certifications. Like the ISO/IEC 25000 quality standard, also called SQuaRE (System and Software Quality Requirements and Evaluation).
- Security checklists. For example, the OWASP secure coding practices checklist and code review checklists.
It’ll enable you to spot and address issues like:
- Web application vulnerabilities caused by insecure coding practices. Is your app secured against all vulnerabilities listed by the latest OWASP top 10? Are payment details stored and processed correctly? These are the questions that this testing strategy will help you answer.
- Network infrastructure weaknesses. Being compliant with PCI DSS implies that your internal network infrastructure handling cardholders’ data is robust enough to it against attacks. Test your network regularly and you’ll be fine.
- Cloud-based applications security flaws. Did you move your applications to the cloud? It’s your responsibility to regularly test all operating systems and apps to identify and minimize security risks.
2. Reactive Software Testing Strategy
This software testing strategy has no prerequisites or standards to abide by as it’s built on defects that emerged after the software has been released. It’s ideal for:
- Already released applications. Are you looking to check the flaws found in the running application to avoid adding more to-dos to your technical debt? This is a good software testing strategy methodology to use.
- Newly written code. Are you working on new code but didn’t yet identify its strengths and weaknesses? Then go with a reactive test strategy. Why? Because Veracode research shows that 32% of applications are released flaws, which only continue to grow in the years after their release.
This reactive approach is fluid and enables you to address defects in released software as they’re discovered in the wild. Exploratory testing (i.e., unstructured, without prepared use cases) is a typical example of a reactive software testing technique.

Exploratory testing works a bit like when we explored the great outdoors as kids. None of us needed a plan, maps, or pre-set rules to have fun, and discover hidden treasures. Developer and QA teams are much the same.
In this strategy, tests are instigated and performed in the later phases of a project, often after release, and/or once vulnerabilities like those listed below have been identified.
- Sensitive data transferred unencrypted. Is the login information being sent through the insecure hypertext transfer protocol (HTTP) instead of going through the more secure hypertext transfer secure protocol (HTTPS)?
- Application bugs. Is the application working as it should? If it isn’t, it might have some bugs.
- Detailed error messages. Are error messages showing too much information that could lead to a data breach, as described under point 15.1 of the RFC2616?
3. Analytical Software Testing Strategy (Risk- or Requirements-Based)
In this methodology, tests are always built on the analyzed risks or requirements. Even the test results are recorded with respect to the same factors. When should you use it? This software test strategy it’s excellent for:
- Critical software products. Let’s say you have to create a critical application handling tons of customers’ sensitive data. To protect those data, the project manager has included in the BRS document specific security requirements and risks. This is where the analytical software testing strategy comes in.
The QA team will have to build tests to ensure the code truly satisfies those requirements.
- Agile Teams. Agile sprints are usually short. To make things worse, after release, the application becomes more complex, requiring every cycle some additional tests. The analytical test strategy can help QA teams choose and prioritize the correct tests based on risks or requirements.
In fact, in this strategy, all tests are based on and prioritized by the BRS document. That’s why they’re useful from the earliest stages of the project (i.e., requirements and design) to the end. They’ll help you verify factors like:
- Data Security. To protect sensitive data from snooping, the application should transfer data between the server and the client encrypted and authenticated with the support of a secure socket layer (SSL)/transport layer security (TLS) certificate. Data at rest should also be encrypted to shield your valuable information from breaches.
- Secure password storage. No passwords should be stored in a database. Only password hashes (i.e., a fixed-length string of hexadecimal characters obtained from running the password through an algorithm[ i.e., a mathematical formula]). The resulting hashes should be salted and peppered to add another layer of security.
- Level of code protection. To protect your application from malware infection and attacks, all codes should be signed with a code signing certificate issued by a trusted certificate authority (CA). This validates your application’s authenticity and originality (i.e., it’s really coming from you), and indicates when there’s tampering (i.e., protects data integrity).

4. Standards- or Process-Compliant Software Testing Strategy
The standard-compliant software test strategy is set up based on standards, guidelines and/or processes. For example, it’s optimal when:
- Project teams follow a standard software development process. Agile, Scrum, you name it. If your organization has implemented a standard software development process, this methodology will make things go even smoother.
- Applications must comply with standard regulations and laws. Does your web application allow online payments and, therefore, you must comply with the previously mentioned PCI DSS standards? Don’t worry; the process compliant test strategy will ensure you’ll achieve it.
Sounds familiar? This type of testing strategy is similar to the methodical one we discussed at the beginning of this section. The key difference? It’s strictly regulated by the standardized policies set by an authoritative body. Like the industry or government standards set by the Food and Drug Administration (FDA) or by a panel of specialists (e.g., the Agile alliance, or the CA/B Forum, IETF, or PKI Consortium in case of PKI infrastructure and digital certificates).
Typically used at both early and late stages of development, it’s hardly customizable. The key items addressed will depend on the set of policies you’ll have to abide by:
- Test frequency. Many industry standards, such as PCI-DSS, require the regular testing of components to keep the application environment secure.
- Tests type. Let’s stick to the PCI-DSS example. Depending on an organization’s size, it must run periodic penetration tests and network penetration tests after a significant change.
- Test methodology. If you’re following the Agile process, you’ll have to ensure that the whole strategy is built around your user stories. This incudes the test criteria, the tests to consider essential, and reporting.
5. Model-Based Software Testing Strategy
This is the type of software testing strategy I used for a machine learning-based security code. It uses ad-hoc created models in a kind of “virtual testing” environment to stress the system and, thus, predict the application’s behavior.
How does it work? The name says it all. It’s based on a model created with the unified modeling language (i.e., UML, a diagram for software systems) or with systems modeling language (i.e., SysML, a diagram for software system applications). It’s excellent for:
- Performance testing. Want to know how scalable your application is? This strategy will let you check your app performance level with a hypothetical growing number of users, or against increased outbound or inbound traffic on your network.
- Security testing. In Q2 2023, Cloudflare observed a 532% surge in denial of service (DDoS) attacks exploiting a vulnerability in Mitel collaboration software. You can build a model of your application to verify and enhance its resistance to this kind of network disruption attack.
As these tests are flexible and can be easily automated, it’s a popular strategy. It’s often implemented during the requirements and design phases of a project and enables teams to verify items like:
- How well your software is protected against malware. What happens if a malicious third party or a user uploads an unsigned file? Will the application accept it and risk a potential malware infection spreading to the whole organization?
- Whether your software is protected against man-in-the-middle attacks. When a user goes to the application login page, is the connection using the secure HTTPS protocol and a valid transport layer security (TLS) certificate?

- Brute force attack resistance. According to Verizon, 74% of data breaches in 2022 involved the use of stolen credentials. What happens when an attacker tests a list of stolen passwords to login into the application? Is there a failed login limit set or not?
6. Regression-Averse Software Testing Strategy
The name says it all. This type of highly automated testing focuses on minimizing the risk of regressions (i.e., making things worse) after implementing a change. How? By testing different use cases, from the most to least common.
This strategy is your best bet against:
- Releasing a new feature that may damage your application. With automated functional and non-functional (i.e., not related to the application’s functionalities) regression tests, it’ll enable you to verify that nothing has broken (i.e., code integrity) before releasing the software.
- Issues caused by an already implemented update. Was an update so urgent that you didn’t have time to test it fully? This sort of testing can be used as a form of post-release verification. You can even choose to focus on only specific components, or test the whole product (e.g., unit testing, system testing).
When you update an application, you want to improve it, not make it worse, right? This software testing strategy is utilized in both early and later stages of the development process and includes checks that’ll identify issues like:
- Use of an insecure code signing certificate. By mistake, instead of using a code signing certificate issued by a trusted CA, a developer selected a self-signed certificate available on its device or an expired certificate. Both oversights may look minimal, but they could be easily exploited by a cybercriminal to infect the application with malware.
- New third-party vulnerabilities. Since 2019, attacks on free repositories like npm and PyPI have increased by 289%. If your latest change included a third-party library or code, you should verify that it hasn’t introduced new vulnerabilities.
- Leak of sensitive information. Are you sure that no one forgot any credentials embedded in the source code? Check it out. GitGuardian identified 67% more hard-coded credentials in 2022 compared to the previous year.
7. Consultative Software Testing Strategy
Also called directed software testing strategy, this approach is usually guided by the most knowledgeable stakeholder (e.g., your internal or external client) and is built around their requirements and ideas. In other words, this knowledgeable user decides what to test and how it’s going to be tested.
I can see raising eyebrows. I know, sometimes it can be difficult to fully understand a client’s requests, but this approach is suitable for:
- Software testing companies. Valued $3.56 billion in 2022, the software testing outsourcing market is booming. Are you working for a software testing company? This is one of the typical software testing strategies you’ll work with.
- Testing software compatibility. Before buying new software, organizations should always ensure it’ll work flawlessly with their systems. How do they do that? By providing their IT teams with a list of items to test for compatibility (e.g., internal applications, antivirus software, etc.).
Examples of what this software testing strategy is used to certify include:
- Which browsers and operating systems are supported. Check that the code works as designed in all browsers the client requested you to support, including mobile-specific browsers. Why is it important? Just to give you an example, the telecom giant Ericsson has recently announced that the global mobile network traffic almost doubled in the last two years. You don’t want your organization or client to miss these potential customers, right?
- Compliance with App stores requirements. Did you know that in 2022 consumers spent an incredible $167 billion buying applications from app stores? Making sure that the code is compliant with the most prominent app stores will probably be one of the most sought requirements by your client.
- Any specific configuration settings that are needed. Ensure that the application is configured as specified by the client (e.g., using the default IDs and passwords isn’t permitted, it accepts as uploads only code signed files).
Et voila’. Now you should have a better idea of what a software testing strategy is. Next, let’s find out what essential elements it should cover.
What Should Good Software Testing Strategies Cover?
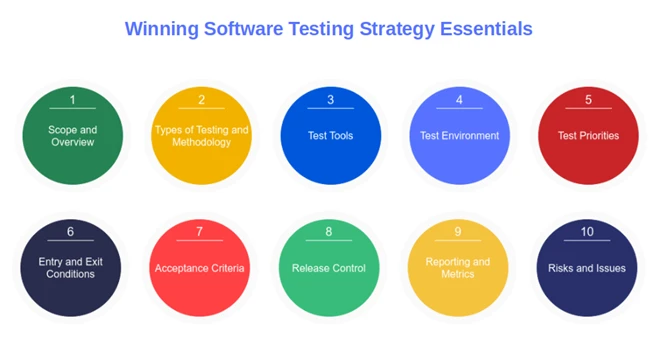
Did you already identify which software testing strategies among the ones we’ve just listed would best fit your project? Good. No matter which one you select, there are some essentials you should always include when drafting your software testing strategy document.
Think of it like building a car. Whether you’re going for a posh, expensive Ferrari or a small city car, some things will always be there (i.e., wheels, a motor, brakes, etc.). The same happens with software testing strategies —certain elements must be included.
1. Scope and Overview
This should be placed at the very beginning of your software testing strategy document and should describe:
- What you want to achieve. Briefly explain your main goals to avoid getting off track or investing resources in unnecessary testing activities.
- A brief overview of testing and project activities. This should include for example, a high-level timeline, testing phases, exclusions (i.e., what isn’t going to be tested), and procedures.
- Information related to the software testing strategy document. Don’t forget to add to your software testing strategy who is responsible for reviewing it and approving it, and a list of related documentation.
2. Types of Tests and Testing Methodologies
In this section you’ll define the key information about the tests that’ll be run during the whole SSDLC and why you’ll run them such as:
- What type of tests are going to be included. List the tests that are going to be performed (e.g., unit tests, integration, regression, usability, acceptance, and/or performance).
- Testing approach and procedures. Do you remember when we talked about the risk and requirement-based software testing strategy? This is where you should describe the approach to take, and the procedures to follow.
- How test changes are going to be handled. Explain in detail the agreed upon change management process and who is going to be responsible for it.
3. Test Tools
List everything needed to run the tests (software and hardware). Such as:
- Tools and software required to execute automated and manual tests. From bug-tracking tools like Bugzilla and Jira to security testing tools like static application security testing (SAST), and dynamic application security testing (DAST) software.
- Specify which tool (or tools) is going to be used for which test. List the tools you’re going to use (e.g., test automation tools), and who will use them.
- Indicate the type of tools used. Are you going to go for proprietary or open source tools? Describe the level of security offered, and the number of users supported.
4. Test Environment
This is another important part that’ll help you accurately define the test environments (i.e., specifically configurated hosts/servers to simulate production conditions enabling the QA team to test the code to identify issues and bugs).
For example, want to make sure your application will work smoothly with all major types of browsers? A cross-browser test environment will let you evaluate it on different browsers and versions. In this category, you’ll therefore mention:
- Where each test is going to take place. Are you planning to perform some tests in a development environment and others in, test, staging, and/or in production environment? Specify this information.
- Information about the chosen test environments. How is each environment (e.g., different devices, operating systems) going to be set up and configured? Is any of those environments going to be linked to a database?
- Back up and restore strategy. In case of data loss (bad luck happens during testing too) what are the backup and restore procedures? Who is in charge?
5. Test Priorities
Why is setting priorities important for your software testing strategy? Think about all the test case scenarios you could come up with for a single application. This is especially true for complex applications, where the number could be immense, requiring significant investments of effort, time, and money.
However, if you prioritize test cases based on risks and requirements, you may be able to limit their amount to the strictly necessary thus, increase efficiency and reduce costs. Therefore:
- Identify the project’s key testing priorities. Are you building an app that is going to handle sensitive information? Your tests will have to focus on security, and vulnerabilities. Is performance essential to your project? Add it to your list.
- Establish priority levels. Categorize critical points by low, high, and critical priority. Don’t forget to add a brief description.
- Weight your crucial functions wisely. In the case of regression tests, base your ranking on the most critical functionality from the business point of view, high-risk vulnerabilities and bugs, and areas with dependencies.
6. Entry and Exit Conditions
Once you’ve determined what tests to execute and how they’re to be conducted, it’s paramount to define entry and exit conditions.
- Establish when the tests should start. The product manager and the stakeholders should establish the conditions and criteria of when the test is going to start (i.e., entry criteria). In the case of unit testing, one of these criteria could be when the requirements have been approved and test units are available.
- Define when a test is considered concluded. The exit criteria should include all the activities needed to complete a specific test phase. Once again, in the example of unit testing, typical exit criteria could be when all critical test cases have passed (more on this in a minute).
- Enumerate the documentation that’ll support the tests. Outline the documentation that’ll support the fulfillment of entry and exit conditions (e.g., test logs, and test summary).
7. Acceptance Criteria
How are you going to decide whether each test has passed? This is exactly what this section is all about, and it should include items like:
- A clear and concise list of the minimum conditions defining if the test passed or not. For example, the code must be signed with a CA-issued code signing certificate. Are you following the Agile methodology? Base your acceptance criteria on user stories.
- Explanation of how those terms are to be measured. Suppose that you’re testing for vulnerabilities. In this case, you may determine that a test will be considered successful only if all critical vulnerabilities have been fixed.
- Additional support information. Providing a set of compelling sample scenarios meeting the criteria or, short checklists will help avoid misunderstandings.
8. Release Control
Ensure the test execution techniques and the release management have been properly, and effectively designed to reduce risks and improve the quality of the code that is going to be released. The section explains:
- Who will be responsible for the release. It includes the names and contact details of the person in charge of the code release.
- The approvals needed before the release. Spell out the approval chain to follow, if the code has to be reviewed before being signed off, and how all these activities are going to be tracked.
- The defined time slot for the release. This way, the QA team will know exactly how much time they’ll have to properly test the code.
9. Reporting and Metrics
OK, the QA team is done with testing. Now what? To whom and how are the testing results and detailed outcomes going to be reported? Are graphics and tables going to be included? What about dashboards? Let’s establish it.
- Determine who will deal with test reporting and communication. Indicate who is going to be responsible for redacting, tracking, and communicating the test results.
- Record who is going to receive and analyze the outcomes. Are the test results going to be shared first with the software developers, and only after a thorough analysis, with the project managers, and/or product managers? Document it to avoid confusion and false expectations.
- Describe in which format the results are going to be reported, and how they’re going to be measured. How are you going to track the number of cases that passed or failed or, the percentage of requirements covered? You may use a common template that includes a test summary report, the execution, defect, coverage, and the test analysis report.
10. Risks and Issues
As the master of horror and supernatural books, Stephen King said, “There is no gain without risk.” The same goes for projects. There’s no project without risks, and just ignoring them would be futile. Therefore:
- List and categorize all possible risks, and issues that could come up during testing. A typical example is when suddenly, one of the most experienced testers is off sick. What are you going to do when you already have limited resources, and time?
- Prepare a mitigation and backup plan for each risk that may occur. In some situations, having a replacement tester trained and ready to step in (e.g., in case someone is sick) can save your bacon.
- Identify a responsible party for executing the backup plan should the worst happen. When you’re in the middle of a test, the last thing you want is to see all those hours spent on it going down the drain because you didn’t have a backup plan.
There you have it. These were the key essential items a top-scoring software testing strategy should encompass. By the way, don’t forget to list the names and roles of those who reviewed and approved the strategy.
Do you want additional guidance to help you create your brand-new software testing strategy? Check out the following resources for further tips and ideas:
- National Institute of Standards and Technology’s (NIST’s) Technical Guide to Information Security Testing and Assessment.
- International Organization for Standardization (ISO)-29119.
- OWASP’s Web Security Testing guide.
- Microsoft’s Testing Strategy Best Practices.
- List of automation frameworks.
So, based on what you’ve discovered today, what is the software testing strategy that you think would work best for your organization and projects?
Final Thoughts on What a Software Testing Strategy Is and What It Should Cover
If you’re aiming to release top-quality and secure products, having a well thought out software testing strategy will put you on the right path. Add to it the OWASP secure coding practices and the code review checklists mentioned in this article, and you’ll immediately see the difference.
Creating a compelling test strategy will help you select the right tests for the right reasons. It’ll make your whole testing system more effective and ensure that the product will be released in production without any major unaddressed issues. Just be sure your strategy covers all the essentials you’ve learned today, including:
- What you’re testing and why,
- Which items should be prioritized,
- In which priority is each risk and security issue going to be addressed, and
- What it’s going to be tested and when.
Remember: A test is only as good as the strategy behind it. Invest some time into developing your software testing strategy, share it with your peers to get their unique perspectives and feedback, and get ready to shine!


