Let’s Encrypt Code Signing Certificate Alternatives

There’s no such thing as a free lunch, but there are viable alternatives to Let’s Encrypt code signing certificates. Find out how you can assert your publisher’s identity and guarantee the integrity of your code without breaking the bank
Let’s Encrypt is a nonprofit digital certificate-issuing body that provides free basic (i.e., domain-validated) secure sockets layer/transport layer security (SSL/TLS) certificates. It’s popular among small businesses and organizations on a tight budget looking to avoid getting their websites flagged as ‘not secure’ by major browsers.
But what if you’re a software developer/publisher looking to prove your code is safe to install and authentic with a code signing certificate? Can you get it from Let’s Encrypt at zero cost, too? No. Let’s Encrypt, like all other vendors, doesn’t offer free code signing certificates.
Don’t give up on your dream of publishing digitally signed, secure code just yet. Keep reading to get everything you need to tap into the global software market that Gartner predicts will be worth over $1 trillion by the end of 2024. Join us in our quest for Let’s Encrypt code signing certificate alternatives that can help you save some bucks without compromising security and service.
Let’s Encrypt Code Signing Certificate Alternatives: How to Avoid Dangerous Workarounds
Software development can be a lucrative business nowadays. Code and apps are everywhere and play a significant role in nearly every part of our lives. However, creating a code or an application, even a basic one, costs time and money, no matter how many corners you cut.
So, with free code signing certificates off the table, firms and developers with limited budgets are left with two feasible possibilities:
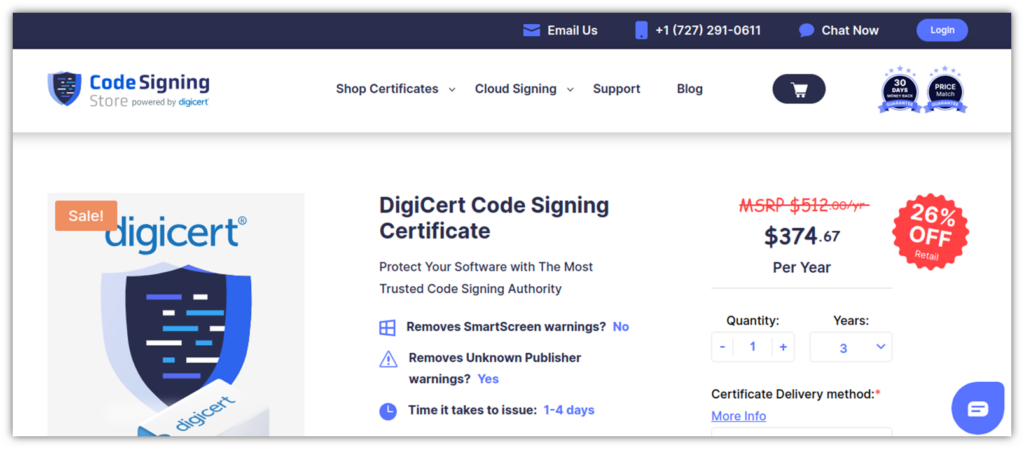
- Purchasing a certificate from an authorized reseller like CodeSigningStore.com or,
- Buying a certificate from a reputed CA.
Save Up to 27% on a Standard Code Signing Certificate
Assert your organization’s verified digital identity to increase trust in your software and updates. Boost your sales and download rates for as little as $195.00/year (with a 3-year certificate).
Both will give you access to standard OV and extended validation (EV) code signing certificates that meet the latest CA/B Forum industry standard. In fact, since June 2023, all certificates’ keys must be saved on a FIPS 140-2 Level 2 or 3-compliant storage (e.g., a USB token or ahardware security module [HSM]). However:
1. Authorized Resellers Offer Highly Discounted Code Signing Certificates
If you have little money, purchasing your code signing certificate from licensed vendors like CodeSigningStore.com may be the best choice. For instance, our Let’s Encrypt code signing certificate alternatives are issued directly from the most trusted CAs, ensuring their authenticity and reliability at an affordable price.
As part of the deal, you’ll also receive guidance on completing the validation process and 24/7 code signing process support.
Other certificate dealers might also have similar offers with a different issuing process or a limited selection of CAs. So, be sure to pick the right retailer that meets your needs and expectations.
2. A Globally Trusted CA May Give You Some Freebies and Extras
Are you willing to pay a premium in exchange for additional services/software and specialized technical support? Go directly to the source. It’ll cost you a bit more, but you’ll also getaccess to perks that might help you save money in the long run. Choose wisely as, once again, not all CAs are equals. Sectigo (and, therefore Comodo CA), for example, doesn’t support Azure Key Vault hardware security module (HSM) key pair storage, while DigiCert will.
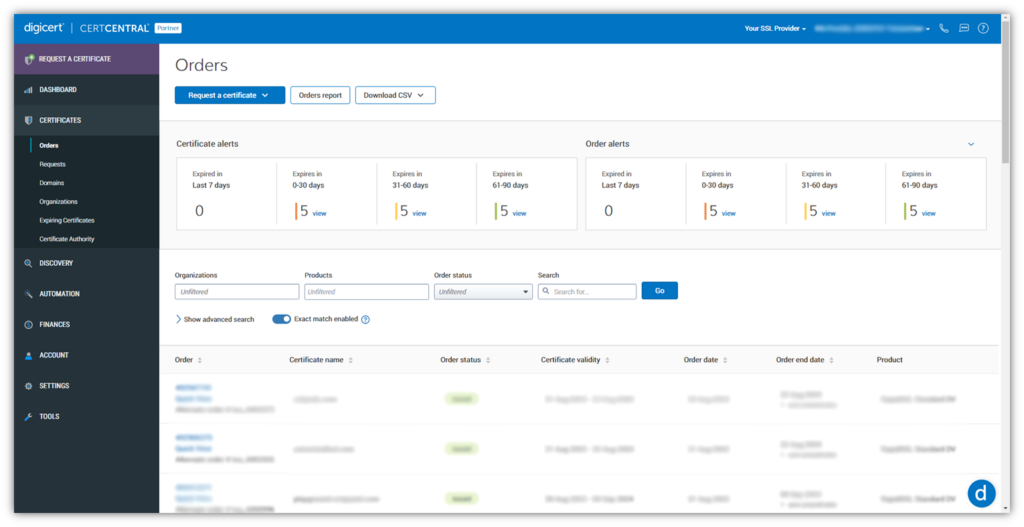
Are you struggling with an increasing number of keys and certificates in your organization’s IT ecosystem, like 72% of organizations interviewed by KeyFactor in 2022? Once again, all DigiCert certificates come with complimentary access to its certificate management platform.
Still undecided? Check out our tips to figure out your best Let’s Encrypt code signing certificate alternative.
But Can’t You Use a Free, Self-Signed Code Signing Certificate?
Relying on self-signed certificates is a dangerous workaround that no self-respecting developer or publisher should consider for public use cases. While self-signed code signing certificates can still be used for internal testing, they’re a no-no for signing release codes. Self-signed certificates:
- Can be generated by anyone (including cybercriminals), and there’s no trusted CA behind it.
- Aren’t trusted by major operating systems and browsers and will trigger all kinds of security alerts.
- Don’t comply with the CA/B Forum industry standard, as the private key can be stored anywhere.
Sounds familiar? I bet it does. Self-signed certificates can be as risky as free DV SSL/TLS certificates, which were used by nearly 75% of phishing sites, according to 2020 data from Fortra PhishLabs. What makes these so attractive to bad guys? The fact that domain validation only proves that someone controls a website — it doesn’t prove that their identity is authentic.
Why All Trusted Let’s Encrypt Code Signing Certificate Alternatives Aren’t Free
DV SSL/TLS and code signing certificates are X.509 digital certificates (i.e., based on public key infrastructure — PKI). However, some substantial differences explain why there aren’t cost-free code signing certificates. Are you into skimming? Have a look at the table below to catch the highlights.
| DV SSL/TSL Certificates | Let’s Encrypt Code Signing Certificate Alternatives | |
| Key Pair Storage | Private Keys are generated and stored on the certificate owner’s server. | Keys must be stored on a FIPS 140-2 Level 2-compliant key storage (as a minimum). |
| Issuing Process | Automatic process. Very fast (issued within minutes). No proof of identity is required. | Man-powered, standard business validation process. Lasts up to 5 days (depending on the CA/vendor). Proof of identity and other documentation required. |
| Security Level | Low. Anyone can get a DV SSL/TLS certificate. | High. Certificates are only issued after a thorough identity validation process. |
Save Up to 21% on a Microsoft Code Signing Certificate
Need an extended validation (EV) code signing certificate to sign drivers? Get your EV certificate today for as little as $277.71/year for a 3-year certificate.
1. Let’s Encrypt Code Signing Certificate Alternatives Must Be Stored on a Secure Hardware Token
Do you remember when we said that all certificates’ keys issued after June 2023 must be stored on secure hardware? I will tell you a not-so-secret secret: that hardware is much safer than a web server, but it also costs money.
You can use your own existing compliant hardware, but if you don’t have such a device, it means you’ll either have to purchase a new secure USB token with your certificate or you’ll have to turn to third-party solutions such as:
Nevertheless, you’ll still have to fork out some dough.
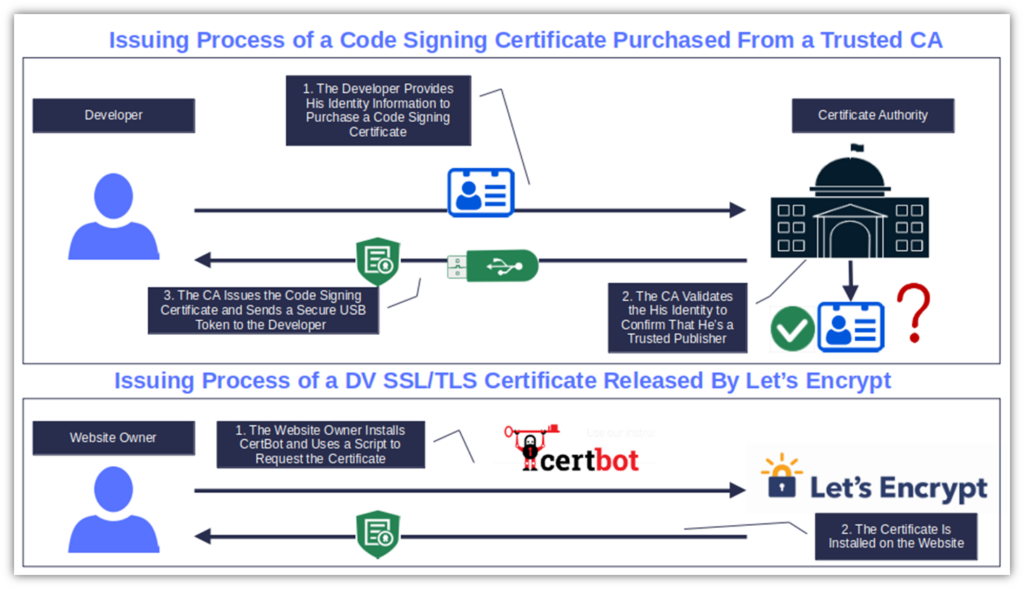
2. Code Signing Issuance Process: Automatic vs. Man-Powered
To issue a DV SSL/TLS certificate, CAs like Let’s Encrypt only ask the requester to prove they have access to the domain they’re buying the certificate for. All they need to do is send a certificate request through a software like Certbot. Done. Anyone can do it, even an unskilled cybercriminal. There’s no need for proof of identity; no validation, and no reason any user should trust the website the certificate was issued to.
Applying for a code signing certificate is a whole other story. The CA must verify that you’re who you say you are and you’re trustworthy. To that end, the CA staff will manually review your official documentation, make verification phone calls, and check other third-party organization records.
All these activities aren’t tasks for machines or artificial intelligence (AI), which is why they cost big bucks in terms of financial resources, human labor, and time.
What’s the point of all this validation hassle? It’s “Elementary, Dear Data,” as one of my favorite Star Trek episodes says.
The CA’s complex validation process and the cost of the certificate itself act as effective barriers against attackers who are looking for easy pickings. Of course, virtually nothing is impossible for a determined cybercriminal, but taking every possible precaution certainly helps.
3. Free Doesn’t Always Mean Secure
Did you know that attackers have been using free DV SSL/TLS certificates for decades, including those issued by Let’s Encrypt? In 2023, fraudulent sites (i.e., phishing) surged by a staggering 90% in just three years. Getting a legit SSL/TLS certificate through an automated process without checks is an easy order for cybercriminals.
OK, not all identified phishing sites had an SSL/TLS certificate installed. However, in 4Q 2023, 55% of the instances of malware discovered by WatchGuard were initially hidden via HTTPS connections.
Security always comes at a price. And now that software-based cyber attacks have become the new normal, signing your software, scripts, and code is something that software publishers can no longer do without. Want a couple of examples? BlackFog recorded a 68% increase in ransomware compared to the previous year. SonicWall identified 6.06 billion malware attacks in 2023.
By attaching your cryptographic digital signature, you can prove the authenticity of your software and help protect your customers’ software supply chains.
Verification and Security: The Power of a Code Signing Certificate Issued by a Trusted CA
Having a CA vouch for you as a trustworthy, reputable organization/developer that creates secure products costs money. There’s no doubt about it. Nevertheless, there are a few advantages that come with paid code signing certificates, and they’re all worth much more than the cost of the certificate itself. Here, we’ve listed three of them.
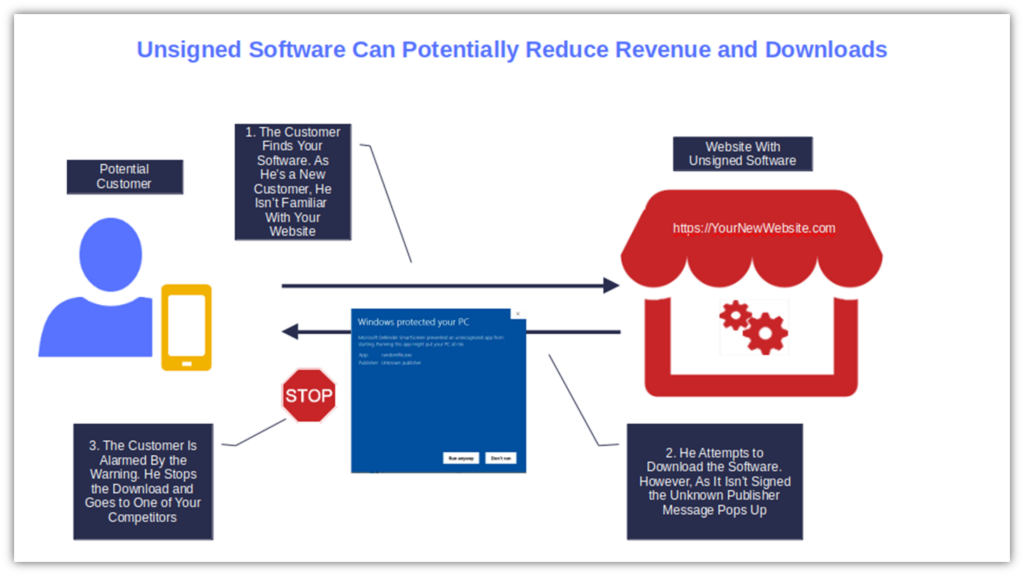
1. Jack Up Your Revenue Opportunities By Using a Let’s Encrypt Code Signing Alternative
Would you install software created by an unknown person or company, or download it from a website you aren’t familiar with? I bet you wouldn’t because doing so would be foolish and dangerous. So, why should you expect your customers to do it?
Edelman’s 2023 Trust Barometer shows that 59% of consumers are more willing to buy from a brand they trust, and 67% are loyal to those brands. Imagine how many users (and sales) you’ll lose because customers don’t trust your unsigned software application. The solution? Put a name on your software with a code signing certificate. Your earnings (and downloads) will reach new heights.
2. Replace Pesky Warnings With Reassuring Identity-Verifying Pop-Ups
“Running this app might put your PC at risk” and “Publisher: Unknown.” These are the kinds of alerts users must deal with when attempting to install unsigned code. They’re enough to scare off even the bravest users.
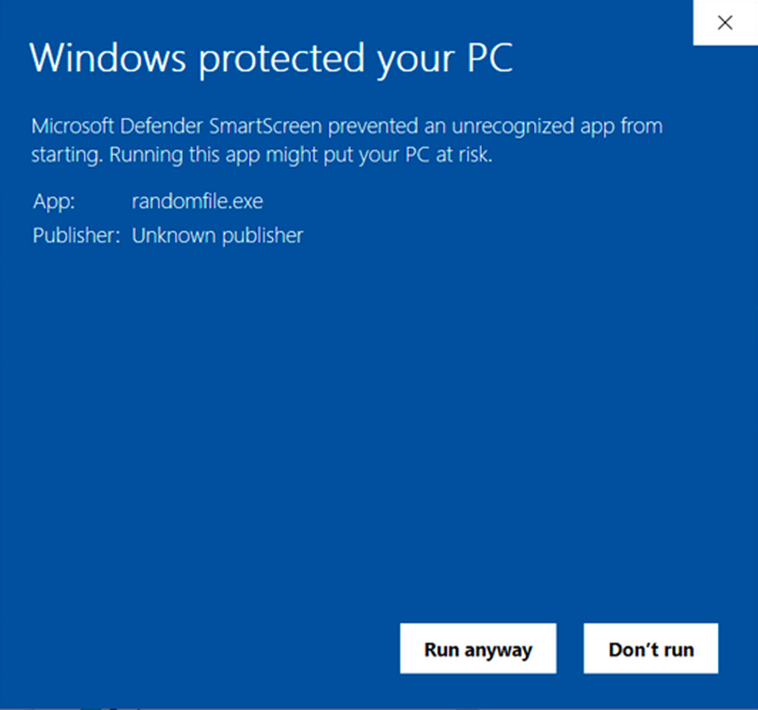
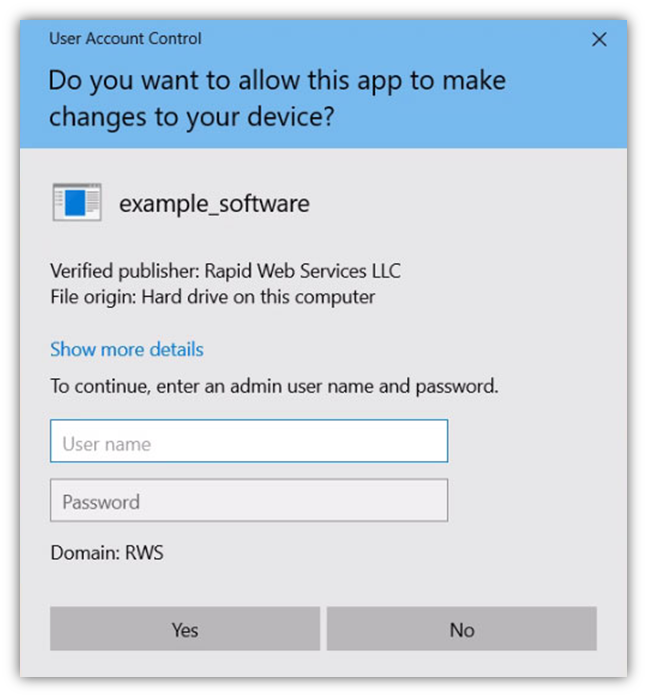
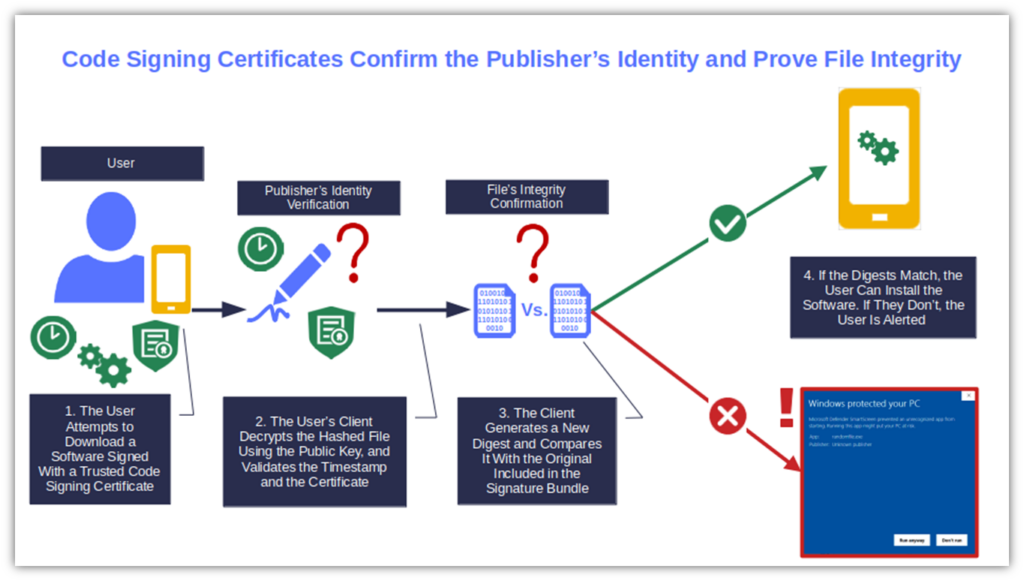
A trusted code signing certificate will transform this alarming message into a positive notification that inspires trust and builds confidence in your brand and products. As soon as your customers click the install button, the User Account Control (UAC) pop-up will confirm that you’re a verified publisher. Your organization’s name will also be displayed in all its glory.
The user’s client will then verify the integrity of the code by generating a new hash (i.e., digest) and comparing it with the original one. If they don’t match, the client will alert the user.
3. Protect Your Business and Users From Costly Malware Infections
According to Arctic Wolf, the average cost of an incident response to a Log4Shell malware attack reached over $90,000 in 2022. Fast forward a meager 12 months, and Cybereason reveals that 46% of companies victim of a ransomware attack estimated a total business loss of up to $10 million.
We know that using a trusted code signing certificate won’t protect you and your customers from all threats. However, it’ll reduce the chances of someone tampering with your software to infect it with malware. It’ll also give users and their Windows devices a way to verify whether someone messed with your software after it was signed. Is saving a few hundred bucks today worth the risk of having to fork out hundreds or even tens of thousands of dollars tomorrow in case of an incident? The answer is up to you to judge.
These points aren’t enough for you? We’ve got more in store. Check out our six reasons why you should release only signed software.
Save Up to 21% on a Microsoft Code Signing Certificate
Need an extended validation (EV) code signing certificate to sign drivers? Get your EV certificate today for as little as $277.71/year for a 3-year certificate.
Final Thoughts About Let’s Encrypt Code Signing Certificate Alternatives
If you want to add a digital signature to your scripts, executables, and other code, you’ll have to purchase a code signing certificate. The good news is that you’ve now learned that you can do that without breaking the bank.
A standard code signing certificate, issued by a trusted CA and purchased from an established vendor like CodeSigningStore.com, is one of the best viable Let’s Encrypt code signing certificate alternatives.
The certificates we sell are heavily discounted, making the annual recurring cost a drop in the bucket compared to the:
- Potential financial impact of a cyber attack, and
- Numerous benefits to guaranteeing your customers a safe product made by a legitimate organization.
Got your new code signing certificate? Great. Did you know that you can also use it to sign Excel macros? Discover how to do it in our next article.


