Step by Step Process: Dual Sign a File with SHA-256 & SHA1 Code Signing Certificate
Signing a file with both SHA-256 & SHA1 Code Signing Certificates using Dual Signing
Sometimes a situation occurs where you must sign an application using two different signatures (hashing algorithms.) For example, if you build an application that runs on both Windows 8 & earlier version like Windows Vista where Windows 8 supports SHA-256, and Windows Vista supports only the SHA-1 hashing algorithm.
To overcome this type of situation you need to first sign an application with SHA-256 Code Signing Certificate and then affix a second signature from SHA-1 code signing certificate. The main reason behind dual signing is to offer support using a single file on previous platforms such as Windows Vista that does not give full support for SHA256 signatures.
To dual sign and include a SHA-1 file on legacy platforms such as Windows Vista use the following commands:
signtool.exe sign /f ExampleCert.pfx /p /t https://timestamp.ca-name.com /v example1.exe signtool.exe sign /f ExampleCert.pfx /p /fd sha256 /tr https://timestamp.ca-name.com/?td=sha256 /td sha256 /as /v example1.exe
For offering full SHA1 signature support two different certificates must be used, here are the commands:signtool.exe sign /f ExampleSHA1Cert.pfx /p /t https://timestamp.ca-name.com /v example1.exe signtool.exe sign /f ExampleSHA256Cert.pfx /p /fd sha256 /tr https://timestamp.ca-name.com/?td=sha256 /td sha256 /as /v example1.exe
Note:
- Here, https://timestamp.ca-name.com contains the Timestamp URL of your Certificate Authority, so add it accordingly.
- You may have to enter extra arguments in signtool.exe such as a password for decrypting the P12/PFX file.
- For dual signing, it’s a must to have the Signtool version 6.3 or above.
Lastly, if you want to support previous Windows platforms such as Windows XP SP2 or earlier, then you have to dual-sign EXEs, DLLs, and other files as well and it will also require a SHA1 based certificate.
signtool.exe sign /f ExampleCert.pfx /t /v example1.exesigntool.exe sign /f ExampleCert.pfx /fd sha256 /tr /td sha256 /as /v example1.exe
Note:
- You may have to enter extra arguments in signtool.exe such as a password for decrypting the P12/PFX file.
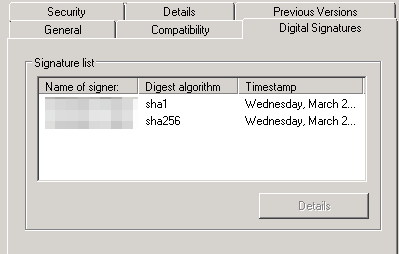
Once the signing is done, it’s best if you verify it. For that follow these steps:
- Select your dual signed application and right click on it and go to Properties.
- From that go to the Digital Signatures tab, and you will find both signing certificates SHA1 and SHA256 & the timestamps for each.